
eWPTX Cert Experiment
Passed INE eWPTXv3 in 7 hours (out of 18). Lab reset once. No XXE or SSTI. Strong emphasis on JWT, SQLi, NoSQLi, deserialization, and CVE exploitation. Below: exam details, my preparation method, a...

Passed INE eWPTXv3 in 7 hours (out of 18). Lab reset once. No XXE or SSTI. Strong emphasis on JWT, SQLi, NoSQLi, deserialization, and CVE exploitation. Below: exam details, my preparation method, a...

Nmap Scan I started by running a full TCP scan on the target using: sudo nmap 10.10.11.74 -T4 -A -open -p- I mapped the domain to the IP in /etc/hosts and discovered a file upload feature accept...

Nmap Scan I started with a full port scan: sudo nmap 10.10.11.83 -T4 -A -open -p- the scan showed a web server running on port 80. There’s a login page and on it, I found an email: jeremy@previo...

Nmap Scan I started by running a full TCP scan on the target using: sudo nmap 10.10.11.87 -T4 -A -open -p- Surprisingly, this didn’t reveal much, so I decided to focus on specific protocols inst...

Machine Information As is common in real life Windows pentests, you will start the TombWatcher box with credentials for the following account: henry / H3nry_987TGV! $User_flag Nmap Scan sudo nmap...

Machine Information As is common in real life Windows pentests, you will start the Fluffy box with credentials for the following account: j.fleischman / J0elTHEM4n1990! Nmap Scan sudo nmap 10.10....

Process Let’s say your target is example.com. You begin with some Google dorking using simple queries, but nothing interesting comes up. After the initial Google Dorking yielded no interesting res...
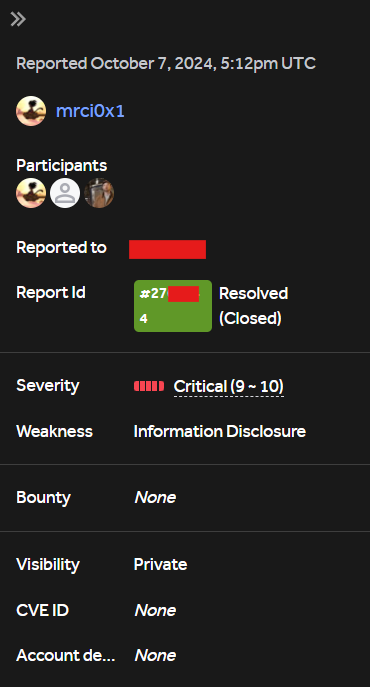
Process One evening, I was exploring the internet like a digital detective, using a Shodan to hunt for hidden clues. Suddenly, I found an open window into a system—a website spilling sensitive inf...
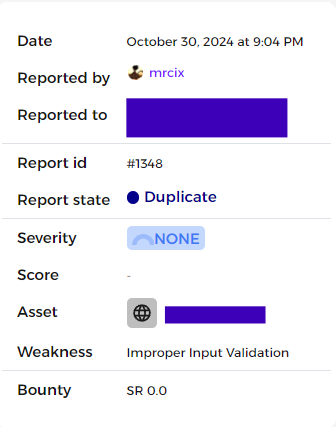
Bypass of Username Policy — Breaking the Rules with a Simple Trick Late one evening, I decided to dive into some bug hunting for a quick session. I noticed the application had strict username rule...