Exposed Sensitive Logs and SQL Queries Revealing User Data
Process
One evening, I was exploring the internet like a digital detective, using a Shodan to hunt for hidden clues. Suddenly, I found an open window into a system—a website spilling sensitive info like logs and fax records, free for anyone to see. No password, no lock, just wide open!
I used a Chrome extension called Hash Extractor to get the favicon hash of the target website. Then, I searched the hash on Favicon Hash Search to find other sites using the same favicon. Finally, I used Shodan to look for potential internal URLs associated with these sites.
It was like finding a secret journal left on a bus, full of private details like emails. I checked just enough to know it was serious, then stepped back to keep things safe.
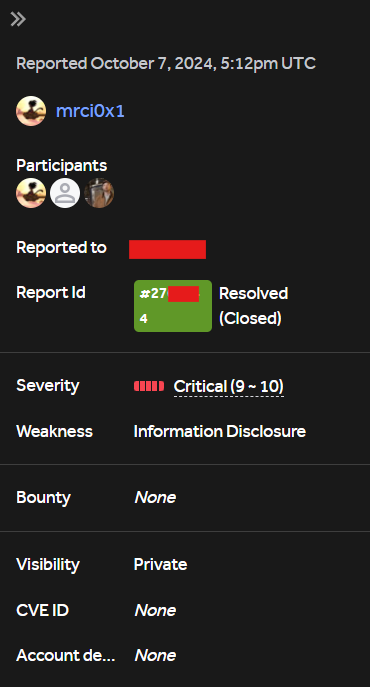
This leak could’ve let hackers steal data or cause big trouble, so I quickly reported it to HackerOne, urging them to seal it shut.